_1.png)
The newly discovered critical security zero-day vulnerability in the widely used Java logging library Apache Log4j is easy to exploit and enables attackers to gain full control of affected servers. Tracked as CVE-2021-44228, the vulnerability is classified as severe, allowing unauthenticated remote code execution. It’s being actively exploited across the globe, and cyberattacks using Log4j continue to grow daily. The vulnerability was reported by Chen Zhaojun of Alibaba Cloud Security Team and disclosed by The Apache Software Foundation on December 9th.
Technical Details of Log4j
The Log4j vulnerability (CVE-2021-44228) triggers because log messages were interpreted as a special language, and one of the abilities of that language is to execute arbitrary Java classes. The result is a powerful remote code execution (RCE) vulnerability. The CVSS score is the highest possible, 10.0.
To remediate this vulnerability, organizations must update all affected instances of Log4j to version 2.15.0. HackerOne is recommending that our customers only consider a version update at this time.
Apache’s official Log4j’s security advisory, including updated information, can be found here.
What HackerOne Has Done Internally
HackerOne identified several internal non-production services we run as tertiary architecture that were impacted by Log4j. We immediately put mitigations in place and patched them when the library updates were released. We believe we are fully remediated and continue to remain alert and vigilant. In addition, through our own Bug Bounty Program, we’ve announced a substantial bounty for any Log4j vulnerability exploits against HackerOne.
What HackerOne is Seeing With Customers
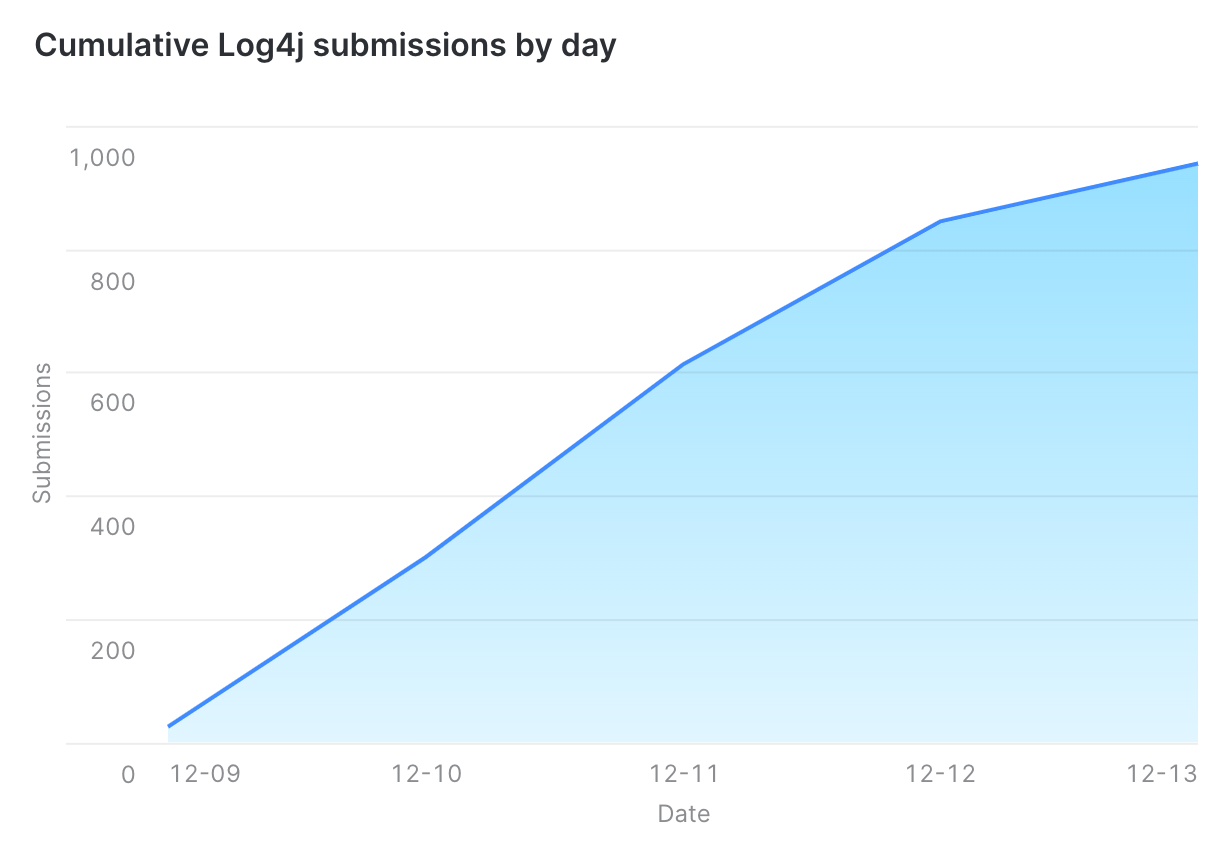
Since the Log4j vulnerability was first reported on December 9, HackerOne has received numerous customer submissions of Log4j vulnerabilities found. These raw numbers may be greater than the number of instances of the vulnerability. See below for graphics of these reports.
HackerOne Report of Log4j Vulnerability Submissions by Day
HackerOne Report of Cumulative Log4J Vulnerability Report Submissions
HackerOne will continue to monitor the Log4j vulnerability and its impact on the industry and our customers. We will regularly post updates regarding this significant cybersecurity event.